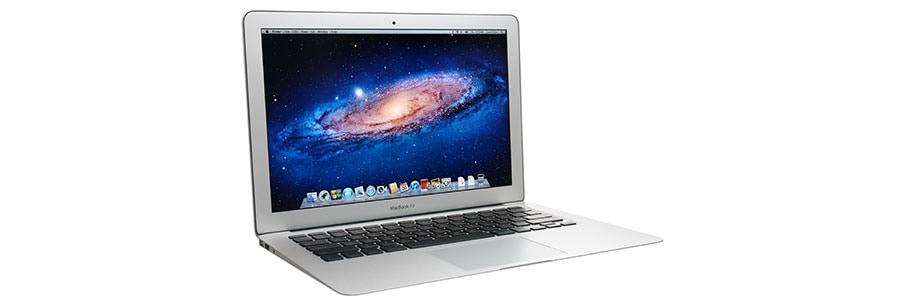
Finally Shed The Old This Year – It’s Costing You Much More Than You Think
New year, new technology! If your business is still relying on older and aging technology, it’s time to think about updating that technology. As it ages, the effort to keep it running comes with many hidden costs. While it may seem financially savvy to keep older hardware and software running, you may be setting yourself